Whether you're a weekend runner gunning for a 5k personal record or an aspiring Olympian with her eye on the medals stand, understanding one's current capabilities is a necessary first step in realizing one's athletic performance goals. Similarly, the first step in achieving—or restoring—the performance of your plant's safety systems begins with a cold-eyed assessment of their current capabilities. Only then can you begin to develop a plan to bring your safety systems to the desired level of performance.
The previous article in this special report ("The Safety Fitness Test"), discussed how to go about assessing the current risk-reduction capabilities of your plant's safety systems, and identifying gaps relative to goal. In this article, we'll focus on applying new safety system technology as a first step toward bringing performance back up to speed.
Through its System 800xA portfolio and more specifically the 800xA High Integrity offering, ABB continues to focus on delivering integrated safety systems solutions worldwide. System 800xA facilitates a fully integrated and optimized system design while also allowing the user to tailor system design and integration concepts to meet plant-specific functional safety management requirements. Further, ABB offers a range of safety system design and engineering services through its Safety Execution Centers worldwide:
- Pressure relief design and calculations
- Safety instrumented system specifications
- Detailed design for up to SIL 3 requirements
- Safety instrumented system delivery, including for emergency shutdown, alarming, fire and gas applications
- Engineers with competence certified by TUV
- Safety Execution Centers around the world, certified by TUV
- IEC61508/61511-compliant functional safety management systems
- Comprehensive systems methodology and documentation
- Commissioning
- Validation
'Proven in Use' Compliance
One of the key advances in safety systems practice promulgated in the IEC's 61508 and 61511 safety standards is the primacy of functional safety management systems (FSMS) for all organizations involved with safety instrumented systems work. This includes those organizations manufacturing the hardware and developing the software; those organizations engineering, installing, testing and validating them; and those organizations operating and maintaining them.
If your plant's safety systems were developed and installed under the aegis of the 61508 and 61511 standards, it's likely that standards compliance was mandated at the project stage. This means that the systems and instruments themselves—as well as the development and engineering organizations behind them—were certified by a third-party agency to conform to the standards.
But for systems that predate the 61508 and 61511 standards (and necessarily their certification to them), standards compliance dictates that users demonstrate safety performance by "proven in use" criteria. This non-trivial task may include retroactively demonstrating the adequacy of the manufacturer's quality management systems in use at the time, a thorough inventory and description of systems components and sub-systems currently in use, and demonstrated performance of these components and sub-systems in similar operating profiles and physical environments. This accumulation of documented evidence must adequately demonstrate that your plant's safety instrumented functions (SIFs)as implemented meet the current safety integrity level (SIL) requirements of your process.
Further complicating the risk profile of older safety instrumented systems is the spreading obsolescence and scarcity of system components, and shortage of personnel qualified to work with them. Indeed, many systems currently in use are beyond their supplier's stated support terms. As a result, "proven in use" compliance or the grandfathering of an older system may be an adequate near-term plan, but continued safety performance will require that many of industry's safety fitness plans incorporate a full system update or upgrade in the not-too-distant future. Indeed, a recent report by the ARC Advisory Group indicates that some two-thirds of the safety systems in use today are at or near the end of their supportable lives.
System Update Considerations
For process plants with older safety instrumented systems, then, the outcome of any responsible safety fitness assessment and planning process is likely not whether to upgrade, but the timing of the inevitable. In the real world, of course, replacing a dated or soon-to-be-obsolete system must take into account risk factors but also financial, production and other resource constraints. But with the decision to upgrade finally made, users face quite a different technology landscape than even 15 years ago.
Today, the bid specifications for more and more new plants include not only compliance with the IEC 61508/61511 standards but also "integrated safety" as a base requirement. While at first blush this contradicts long industry practice of ensuring diversity by physically separating safety systems from basic process control systems, new technology together with users' desire to reduce costs and improve productivity are fueling an industry-wide movement to integrated systems.
Integration, or at least "interfacing," of safety instrumented systems with basic process control systems is in fact not a new practice. Indeed, the IEC standards' non-prescriptive language doesn't rule out even the physical integration of control and safety in the same box or on the same network. Rather, the standards assert that functional safety cannot be compromised by a failure or by maintenance activities associated with the basic process control system.
Diagnostics technology, meanwhile, has advanced in its ability to intercept dangerous faults, and some of today's integrated safety alternatives feature embedded diversity in hardware and software that reach all the way back to separate development teams. As a result, some of today's integrated safety system options can meet demanding SIL 3 application requirements even without the use of hardware redundancy.
"Process safety systems suppliers continue to cost reduce their hardware offerings and integrate their safety solutions with basic process control systems," wrote Barry Young, principal analyst for the ARC Advisory Group in a recent report on the global safety systems market. "Suppliers offering a truly integrated offering of process and safety are saving end users substantial project costs in engineering and lifecycle expense," he said.
With current technology a range of separate, interfaced or integrated solutions are possible among process control system and safety system suppliers (see "Integrated Safety: The Four Architecture Options" below). The most highly evolved option—an integrated platform from a single supplier that is designed from the ground up to perform both safety and control functions—is typified by the ABB System 800xA process automation platform.
Integrated Safety: The Four Architecture Options
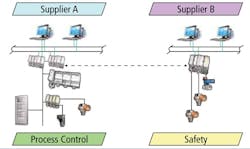
A system architecture based on completely separate basic process control systems (BPCS) and safety instrumented systems (SIS) from different suppliers, typically with a limited, OPC- or Modbus-based link between the two systems, was once the preferred way to incorporate safety systems into the overall plant automation scheme. Physical separation and different development teams helped to minimize common cause and systemic failures, but a custom interface between the two systems introduces an additional set of development and maintenance concerns. Further, different engineering tools and HMI methodologies increase complexity and training requirements as well as limiting operational visibility and synergy between the two systems.
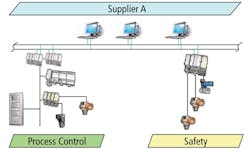
Another typical architecture is the result of an overall automation system delivery from a single supplier but with different BPCS and safety systems. Both systems are based on in-house products, but have been developed separately (or added to the product portfolio through acquisition) without any significant commonalities. The potential for common cause and systemic failures are addressed as with systems from different suppliers, but a common HMI and more rigorous connectivity will likely help operators be more effective and reduce interface maintenance costs. Engineering tools are likely to remains separate, however, allowing for little improvement with regard to training needs or productivity.
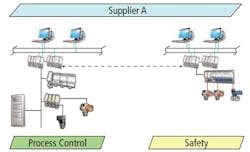
Another system architecture option features similar systems from the same supplier, deployed as two separate systems for BPCS and safety functions. This approach requires that safeguards be in place on the supplier side to ensure that sources of potential common mode and systemic failures are identified, engineered out of the system design or otherwise addressed and managed. And while a similar set of engineering tools and operational displays will boost familiarity and reduce training costs, two separate systems—and all the management discipline involved with them—will need to be separately maintained, resulting in less than optimal engineering productivity. Also, since the two systems share a common heritage, the integrity of the communications link between the two systems should not be a concern.
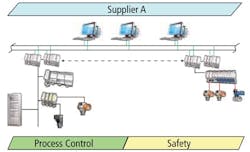
The final architecture option is a fully integrated BPCS and safety system, designed from the ground up to simultaneously satisfy the requirements of both realms. This option is based on, in principle, common hardware and software but using diverse technology and implemented as one system. In addition to sharing the advantages of separate but similar BPCS and safety systems (with similar qualifications), the integrated solution can further leverage the commonalities between the two systems. Common engineering tools and HMI reduce engineering times as well as contribute to more effective operations while maintaining functional independence. This approach allows information management, asset management and production management to be operated across the entire automation platform.
Because it performs as a single integrated system, it features both high- and low-level integration of control and safety system components without compromising the performance of either. Further, taken separately, the ABB High Integrity safety instrumented system can be deployed with control systems from other suppliers either in standalone mode or with top-end integration.
The 800xA platform with 800xA High Integrity safety system functionality features common engineering and visualization tools for both process control and safety functions, boosting both engineering efficiency and operator effectiveness. The integrated approach also allows functions such as information management, asset management and production management to be fully leveraged across the entire automation system. The ABB approach even enables certified safety controllers that can run both process control and safety applications simultaneously—a feature that in some high speed applications can both optimize safety and control performance while reducing capital and hardware needs.
Robust Safety with Lower Project Costs
While the safety components of an integrated environment must adhere to the design, testing, validation and certification processes applicable to safety systems, an integrated approach to control and safety functions can cut capital costs by eliminating some redundant aspects of independent safety and control networks. A smaller system footprint, a unified engineering environment and elimination of a custom interface between the control and safety systems also contribute to project savings.
With the ABB System 800xA, users can decide how much separation to maintain between safety and process control. Even if fully segregated systems are chosen, many residual benefits apply. For example, potential sources of common cause failure already have been analyzed and minimized during the design phase by the development team and independently reviewed by the assessor during the certification of the product. This effectively makes the system smarter and safer from the day it's turned on.
Further, integrated testing is performed during the design validation and verification test, which includes network security as part of the test protocol. Version control, compatibility and interoperability testing are included in the release procedure. The result is a set of common best practices resulting in implementation of an integrated safety system that costs less, works better and even extends the capabilities of the process control system.
In the case of ABB's System 800xA, access control and security are built into the system as an off-the-shelf set of features, including user privileges, user action validation and a common audit trail. It also includes such extended capabilities as write protection, SIL access control and authorization, bypass management, and override mechanisms. The result is a robust set of security controls that apply uniformly across all systems.
As safety systems get replaced, or as new projects are developed, there is an opportunity to decide how you want to address safety in your operation—not just today but for years into the future. Integrated safety can deliver significant performance and cost benefits not only during the project phase, but during the entire operating life of the system. And that's the safety system lifecycle phase that we'll discuss in the final article in this series: Once your safety system is running at peak performance, how can you keep performance from degrading over the next 20 years it's likely to be in use?
Latest from Safety Instrumented Systems

Leaders relevant to this article: