Could Cyber Terrorists Attack Our Company?
By John Cusimano, Director, Exida Security Services Division
and
Eric Byres, Chief Technology Officer, Byres Security
Maybe, but perhaps this isn't the best question to ask. When cyber-related events cause outages and plant shutdowns—whether they were caused by accident, employee, hacker or terrorist—the first question should be, "What made our system unstable and susceptible, and what can we do to prevent it from happening again"?
Some recent headlines have read: "Electricity Grid in U.S. Penetrated By Spies," "China and Russia Hack into U.S. Power Grid," "Russian Hackers Vandalize BTC Pipeline Data Servers," and most recently, "CIA Director Says Cyber Attack Could Be Next Pearl Harbor." With news like this how can anyone sleep at night?
The reality is that most of what is published regarding control system cybersecurity in mainstream media is over-dramatized. While the scenarios painted in these stories may be valid, they are often void of detail regarding these so-called incidents. The result is that the government, public, media and control system operators can end up focusing on possible "long shot" perpetrators and not on the very real day-to-day risks of modern network-based control systems.
The fact is control system cyber incidents are real and are occurring on a regular basis in industries around the world. How do we know? One way is through a service provided by the Security Incidents Organization. It maintains a database called the Repository of Industrial Security Incidents (RISI, www.securityincidents.org) that tracks incidents of a cybersecurity nature that directly affect industrial SCADA and process control systems. By studying actual incidents, RISI helps provide a realistic assessment of the threats and vulnerabilities of our industrial control systems.
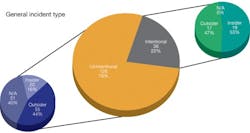
A key finding of RISI is that, while they have occurred, there haven't been a tremendous number of deliberate cyber attacks on industrial control systems. Less than 25% of the incidents recorded in the database represent intentional attacks on control systems. The remaining 75% of the incidents were unintentional.
Whew! Now can we all breathe a sigh of relief? No, not really. While these incidents may have been unintentional they still resulted in downtime, production losses, environmental damage, equipment damage and even injury and death. Unintentional incidents can lead to the same set of consequences. So, while the threats might be different, the vulnerabilities are the same.
These unintentional incidents range from malware (viruses, worms, etc.) to network disturbances to software bugs. The point is that, whether or not you believe your digital control systems may the target of cyber attack, you sure as heck should believe that they are susceptible to a cyber incident.
For example, consider the 44% percent of unintentional incidents that RISI reported were attributed to an outsider. The outsider in the case of an unintentional incident is usually the malware author. An energy company in Australia learned about this the hard way when it was infected with the W32.CF virus. Even if the virus didn't "intend" to infect that energy company, the infection forced the company to restructure all of its 1000 desktops—an expensive proposition. Fortunately, in this case, the virus did not make its way into the control system. Other companies have not been so lucky. Either through connections into the business network, VPN dial-up connections for remote support or even USB drives, viruses have made their way into control system networks. Operator HMIs, engineering workstations, data servers, historians, etc. can all be affected. There are numerous incidents recorded in RISI of such infections that have cost organizations millions of dollars in downtime. Viruses have even been a contributing factor to more serious incidents by preventing operators from seeing critical alarms in a timely manner.
Another 40% percent of unintentional cyber incidents recorded in RISI were not even caused by a person, but rather by faulty equipment or software. These "accidental" incidents have resulted in major operational impacts, such as the computer glitch that caused a major power outage in the Phoenix, Ariz., region. In this case, the power provider, the Salt River Project (SRP), had a system in place to shed load if it was unable to meet demand. Unfortunately, while SRP had no problem meeting load demands on the day of the incident, a computer problem indicated that it did, and, consequently, triggered a widespread outage. An estimated 92,000 Salt River Project customers were without power for 20 to 30 minutes.
RISI contains many, many more examples of both intentional and unintentional cyber incidents. Each one provides a valuable lesson that can be used to avoid similar incidents in your facilities. Furthermore, many of them provide valuable information to manufacturers of automation system equipment on the bugs and vulnerabilities that have been exploited in existing products.
The good news for those willing to address the issue is that even a modest effort can lead to substantial improvements. Numerous organizations have published standards and guidelines to help their constituents bolster the cybersecurity of their installed systems. What you'll find in most of these is not "rocket science," but good engineering practices developed by people in the industry who have learned from experience. For example, ISA99 has completed its ANSI/ISA-99.02.01-2009 standard, "Security for Industrial Automation and Control Systems: Establishing an Industrial Automation and Control Systems Security Program." This standard outlines a straightforward approach that companies can adopt to managing the security lifecycle of their automation systems. Although in a different format, it addresses the same topics as the NERC CIP standards that have been mandated in the United States for all entities that own or operate assets that are critical to the reliability of the bulk electric system.
The best place to start is by performing a control system cybersecurity assessment on your existing systems. Organizations can perform a self-assessment or hire an experienced third party to assist and provide recommendations. We recommend end users work closely with their automation system equipment suppliers because their products play a critical role in the implementation and enforcement of the technical controls called for in security standards.
A key point in any assessment is not to get stuck on low-probability, complex "terrorist" scenarios, but rather to consider the full spectrum of network issues and effects that could harm your operations. For example, what would happen if an everyday virus was carried into the control system in a contractor's laptop? What would be the impact if that virus caused all the HMIs to fault at the same time? Would the plant be shut down, or could it be run "blind," and who would decide? What would the process be to diagnose the problem? What procedures would be used to recover HMIs as fast as possible? What would the process be to prevent the recovered HMIs from being infected again?
You can see that the list can get very long, but all of these questions (and more) are basic ones that need to be asked for each possible scenario. By creating a well thought-out "threat model" that names all the pathways into the control system, all the possible impacts or events and all the possible consequences, a systematic assessment is both possible and cost-effective.
[javascriptSnippet]